Added January 26, 2022: All lists provided on this page are no longer updated.
Windows 10 collect and transmit telemetry data to Microsoft. Telemetry data might include sensitive information. So let's refuse Microsoft servers with the firewall and get peace of mind.
Use one out of the following three methods on this page. (pf, iptables, Windows Firewall)
- pf table for OpenBSD/FreeBSD:
- pf_windows_privacy_us.txt (United Status IPv4)
- pf_windows_privacy_de.txt (Deutschland IPv4)
- pf_windows_privacy.txt (Nippon/Japan IPv4)
pf_windows_privacy_ww.txt (World IPv4)DELETEDpf_windows_privacy_ww_opt.txt (World IPv4 Optimized)DELETED
- pf_windows_privacy_us_ipv6.txt (United Status IPv6)
- pf_windows_privacy_de_ipv6.txt (Deutschland IPv6)
- pf_windows_privacy_ipv6.txt (Nippon/Japan IPv6)
pf_windows_privacy_ww_ipv6.txt (World IPv6)DELETED
- iptables rule file for Linux:
- iptables_windows_privacy_us.txt (United Status)
- iptables_windows_privacy_de.txt (Deutschland)
- iptables_windows_privacy.txt (Nippon/Japan)
- Windows PowerShell script for Windows Firewall:
- winfirewall_windows_privacy_us.ps1 (United Status)
- winfirewall_windows_privacy_de.ps1 (Deutschland)
- winfirewall_windows_privacy.ps1 (Nippon/Japan)
These files are updated every day.
Added January 26, 2022: All lists provided on this page are no longer updated.
And
Add following hosts to your c:\Windows\System32\drivers\etc\hosts
0.0.0.0 3h88yg-sn3302.files.1drv.com 0.0.0.0 3h9byg-bn1305.files.1drv.com 0.0.0.0 3h9k8a-sn3302.files.1drv.com 0.0.0.0 3hp0na-sn3302.files.1drv.com 0.0.0.0 3hpona-sn3302.files.1drv.com 0.0.0.0 3hpzna-sn3302.files.1drv.com 0.0.0.0 3hqehq-sn3302.files.1drv.com 0.0.0.0 5wabhq-sn3302.files.1drv.com 0.0.0.0 5wyvsw-sn3302.files.1drv.com 0.0.0.0 5wzzna-sn3302.files.1drv.com 0.0.0.0 ezru1w-sn3302.files.1drv.com 0.0.0.0 eztgqq-sn3302.files.1drv.com 0.0.0.0 eztjba-sn3302.files.1drv.com 0.0.0.0 fakiwq-sn3302.files.1drv.com 0.0.0.0 fakzyw-sn3302.files.1drv.com 0.0.0.0 famlpw-sn3302.files.1drv.com 0.0.0.0 files.1drv.com 0.0.0.0 g1da1a-sn3302.files.1drv.com 0.0.0.0 g1doyg-sn3302.files.1drv.com 0.0.0.0 q6untq-sn3302.files.1drv.com 0.0.0.0 qdab2a-sn3302.files.1drv.com 0.0.0.0 r30ysg-sn3302.files.1drv.com 0.0.0.0 r33ubq-sn3302.files.1drv.com 0.0.0.0 svj7qa-sn3302.files.1drv.com 0.0.0.0 svjfvw-sn3302.files.1drv.com 0.0.0.0 svkxkq-sn3302.files.1drv.com 0.0.0.0 svlneg-sn3302.files.1drv.com 0.0.0.0 img-s-msn-com.akamaized.net 0.0.0.0 static-global-s-msn-com.akamaized.net 0.0.0.0 static-spartan-eas-s-msn-com.akamaized.net 0.0.0.0 fp-afd.azureedge.net 0.0.0.0 fp-as.azureedge.net 0.0.0.0 fp-vp.azureedge.net 0.0.0.0 fp-vs.azureedge.net 0.0.0.0 c585cd315cbaa96582735b28552b80af.clo.footprintdns.com 0.0.0.0 moiafdazure.clo.footprintdns.com 0.0.0.0 moiazureorigin.clo.footprintdns.com 0.0.0.0 m.hotmail.com 0.0.0.0 blu402-m.hotmail.com 0.0.0.0 skype-m.hotmail.com 0.0.0.0 bn2ap002.device.ra.live.com 0.0.0.0 cid-88cb63afc66ce711.users.storage.live.com 0.0.0.0 device.ra.live.com 0.0.0.0 directory.services.live.com 0.0.0.0 nexusrules.officeapps.live.com 0.0.0.0 s.gateway.messenger.live.com 0.0.0.0 sn3302.storage.live.com 0.0.0.0 ssw.live.com 0.0.0.0 storage.live.com 0.0.0.0 asia.smartscreen-prod.microsoft.com 0.0.0.0 browser.pipe.aria.microsoft.com 0.0.0.0 checkappexec.microsoft.com 0.0.0.0 continuum.dds.microsoft.com 0.0.0.0 cs.dds.microsoft.com 0.0.0.0 emdl.ws.microsoft.com 0.0.0.0 mediaredirect.microsoft.com 0.0.0.0 mobile.pipe.aria.microsoft.com 0.0.0.0 nav.smartscreen.microsoft.com 0.0.0.0 ris.api.iris.microsoft.com 0.0.0.0 sci1-1.am.microsoft.com 0.0.0.0 sci2-1.am.microsoft.com 0.0.0.0 settings-win.data.microsoft.com 0.0.0.0 settings.data.microsoft.com 0.0.0.0 store-images.microsoft.com 0.0.0.0 store-images.s-microsoft.com 0.0.0.0 a-0001.a-msedge.net 0.0.0.0 a-0002.a-msedge.net 0.0.0.0 a-0003.a-msedge.net 0.0.0.0 a-0004.a-msedge.net 0.0.0.0 a-0005.a-msedge.net 0.0.0.0 a-0006.a-msedge.net 0.0.0.0 a-0007.a-msedge.net 0.0.0.0 a-0008.a-msedge.net 0.0.0.0 a-0009.a-msedge.net 0.0.0.0 a-0010.a-msedge.net 0.0.0.0 a-0011.a-msedge.net 0.0.0.0 a-0012.a-msedge.net 0.0.0.0 a-0013.a-msedge.net 0.0.0.0 a-0014.a-msedge.net 0.0.0.0 a-0015.a-msedge.net 0.0.0.0 a-0016.a-msedge.net 0.0.0.0 a-0017.a-msedge.net 0.0.0.0 a-0018.a-msedge.net 0.0.0.0 a-0019.a-msedge.net 0.0.0.0 a-0020.a-msedge.net 0.0.0.0 a-0021.a-msedge.net 0.0.0.0 a-ring-fallback.msedge.net 0.0.0.0 a-ring.msedge.net 0.0.0.0 c-ring.msedge.net 0.0.0.0 client-office365-tas.msedge.net 0.0.0.0 eafddirect.msedge.net 0.0.0.0 evoke-windowsservices-tas.msedge.net 0.0.0.0 fp.msedge.net 0.0.0.0 k-ring.msedge.net 0.0.0.0 l-ring.msedge.net 0.0.0.0 ocos-office365-s2s.msedge.net 0.0.0.0 s-ring.msedge.net 0.0.0.0 segments-s.msedge.net 0.0.0.0 spo-ring.msedge.net 0.0.0.0 t-ring.msedge.net 0.0.0.0 arc.msn.com 0.0.0.0 cdn.content.prod.cms.msn.com 0.0.0.0 0.133.13.11.23.rst5.r.skype.net 0.0.0.0 0.204.8.11.23.rst7.r.skype.net 0.0.0.0 a.config.skype.com 0.0.0.0 api.asm.skype.com 0.0.0.0 api.cc.skype.com 0.0.0.0 api.mcr.skype.com 0.0.0.0 api.skype.com 0.0.0.0 avatar.skype.com 0.0.0.0 b.config.skype.com 0.0.0.0 config.edge.skype.com 0.0.0.0 config.skype.com 0.0.0.0 edge.skype.com 0.0.0.0 etag-rr.prod.registrar.skype.com 0.0.0.0 prod.registrar.skype.com 0.0.0.0 registrar-rr.prod.registrar.skype.com 0.0.0.0 skypexbox.skype.com 0.0.0.0 dsn1.d.skype.net 0.0.0.0 dsn10.d.skype.net 0.0.0.0 dsn11.d.skype.net 0.0.0.0 dsn12.d.skype.net 0.0.0.0 dsn13.d.skype.net 0.0.0.0 dsn14.d.skype.net 0.0.0.0 dsn15.d.skype.net 0.0.0.0 dsn16.d.skype.net 0.0.0.0 dsn2.d.skype.net 0.0.0.0 dsn3.d.skype.net 0.0.0.0 dsn4.d.skype.net 0.0.0.0 dsn5.d.skype.net 0.0.0.0 dsn6.d.skype.net 0.0.0.0 dsn7.d.skype.net 0.0.0.0 dsn8.d.skype.net 0.0.0.0 dsn9.d.skype.net 0.0.0.0 api.taboola.com 0.0.0.0 images.taboola.com 0.0.0.0 client.wns.windows.com 0.0.0.0 HK2SCH130020629.wns.windows.com 0.0.0.0 HK2SCH130020732.wns.windows.com 0.0.0.0 HK2SCH130020829.wns.windows.com 0.0.0.0 HK2SCH130020832.wns.windows.com 0.0.0.0 HK2SCH130021127.wns.windows.com 0.0.0.0 HK2SCH130021535.wns.windows.com 0.0.0.0 skydrive.wns.windows.com 0.0.0.0 comments.xboxlive.com 0.0.0.0 device.auth.xboxlive.com 0.0.0.0 dlassets-ssl.xboxlive.com 0.0.0.0 dlassets.xboxlive.com 0.0.0.0 musicdelivery-ssl.xboxlive.com 0.0.0.0 profile.xboxlive.com 0.0.0.0 settings-ssl.xboxlive.com 0.0.0.0 skypexbox.skype.com 0.0.0.0 social.xboxlive.com 0.0.0.0 title.auth.xboxlive.com 0.0.0.0 title.mgt.xboxlive.com 0.0.0.0 user.auth.xboxlive.com 0.0.0.0 xsts.auth.xboxlive.com 0.0.0.0 api.onedrive.com 0.0.0.0 azwancan.trafficmanager.net 0.0.0.0 bling2.midasplayer.com 0.0.0.0 candycrushsoda.king.com 0.0.0.0 cdn.onenote.net 0.0.0.0 clientconfig.passport.net 0.0.0.0 config.scm.windowsphone.com 0.0.0.0 king.com 0.0.0.0 ocsp.msocsp.com 0.0.0.0 ocsp.omniroot.com 0.0.0.0 www.msftconnecttest.com
How to edit Hosts file.
Right click the start button. Left click the "Command prompt (administrator)" or "Windows PowerShell(administrator)".
cd drivers\etc [Enter] notepad hosts [Enter]
Edit and save.
Usage of Windows PowerShell script
Download above links.
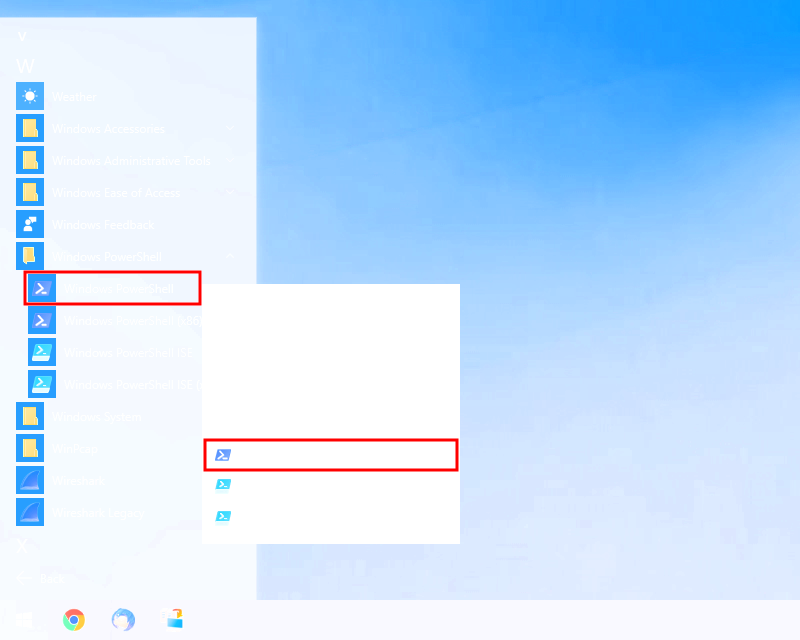
Left click on the Start button.
Select [All apps].
Find [Windows PowerShell] and open nest menu. Left click on the [Windows PowerShell].
Right click on the [Run as Administrator].
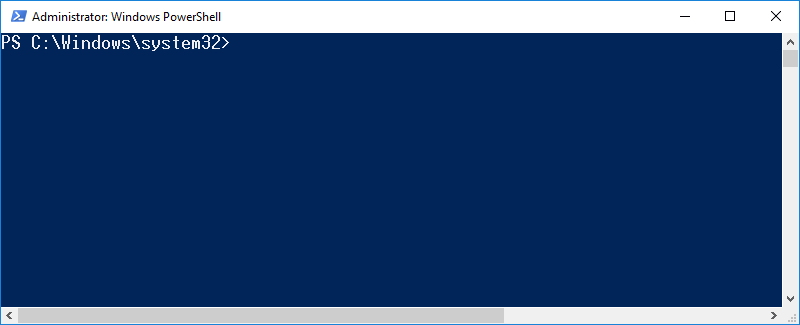
PS C:\Windows\system32> Get-ExecutionPolicy
Restricted
Enter "Get-ExecutionPolicy" and [Enter].
Check the result.
PS C:\Windows\system32> Set-ExecutionPolicy Unrestricted Execution Policy Change The execution policy helps protect you from scripts that you do not trust. Changing the execution policy might expose you to the security risks described in the about_Execution_Policies help topic at http://go.microsoft.com/fwlink/?LinkID=135170. Do you want to change the execution policy? [Y] Yes [A] Yes to All [N] No [L] No to All [S] Suspend [?] Help (default is "N"): y PS C:\Windows\system32>
Enter "Set-ExecutionPolicy Unrestricted" and [Enter].
Enter "y" and [Enter].
PS C:\Windows\system32> ~\downloads\winfirewall_windows_update_us.ps1 Security warning Run only scripts that you trust. While scripts from the internet can be useful, this script can potentially harm your computer. If you trust this script, use the Unblock-File cmdlet to allow the script to run without this warning message. Do you want to run C:\Users\foobar\downloads\winfirewall_windows_update_us.ps1? [D] Do not run [R] Run once [S] Suspend [?] Help (default is "D"): r
Enter "~\downloads\winfirewall_windows_update_us.ps1" and [Enter].
Enter "y" or "a" and [Enter].
Name : {bbf4a6cc-7d38-4825-ac25-9bad3d44f033}
DisplayName : Windows10Privacy_Inbound
Description : https://gato.intaa.net/net/windows_privacy_filter
DisplayGroup :
Group :
Enabled : True
Profile : Any
Platform : {}
Direction : Inbound
Action : Allow
EdgeTraversalPolicy : Block
LooseSourceMapping : False
LocalOnlyMapping : False
Owner :
PrimaryStatus : OK
Status : The rule was parsed successfully from the store. (65536)
EnforcementStatus : NotApplicable
PolicyStoreSource : PersistentStore
PolicyStoreSourceType : Local
Name : {6515e352-8561-401e-a62d-e9d79b28760b}
DisplayName : Windows10Privacy_Outbound
Description : https://gato.intaa.net/net/windows_privacy_filter
DisplayGroup :
Group :
Enabled : True
Profile : Any
Platform : {}
Direction : Inbound
Action : Allow
EdgeTraversalPolicy : Block
LooseSourceMapping : False
LocalOnlyMapping : False
Owner :
PrimaryStatus : OK
Status : The rule was parsed successfully from the store. (65536)
EnforcementStatus : NotApplicable
PolicyStoreSource : PersistentStore
PolicyStoreSourceType : Local
PS C:\Windows\system32>
An outbound rule and an inbound rule are loaded.
Check results.
PS C:\Windows\system32> Set-ExecutionPolicy Restricted Execution Policy Change The execution policy helps protect you from scripts that you do not trust. Changing the execution policy might expose you to the security risks described in the about_Execution_Policies help topic at http://go.microsoft.com/fwlink/?LinkID=135170. Do you want to change the execution policy? [Y] Yes [A] Yes to All [N] No [L] No to All [S] Suspend [?] Help (default is "N"): y PS C:\Windows\system32>
Enter "Set-ExecutionPolicy Restricted" and [Enter].
Enter "y" and [Enter].
Remember this.
Right click on the Start button.
Left click on the [Control Panel].
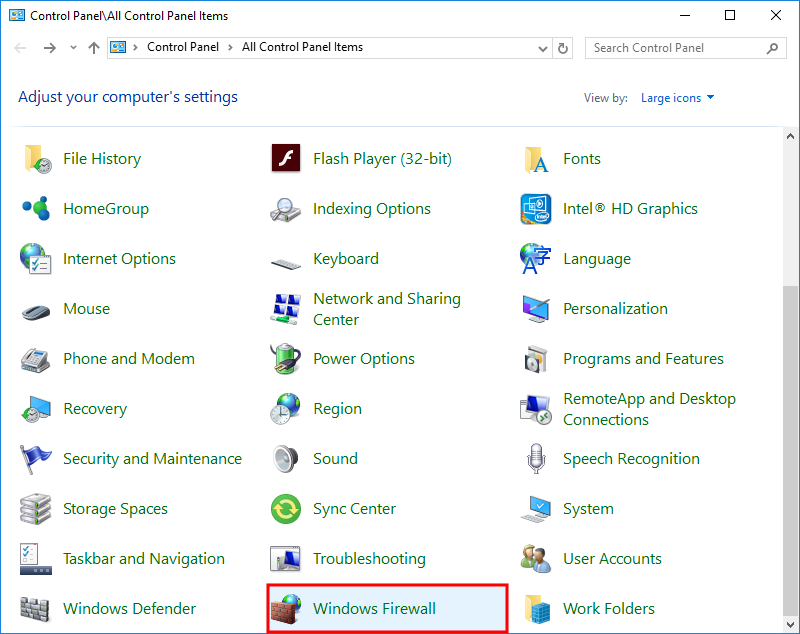
Left click on the [Windows Firewall].
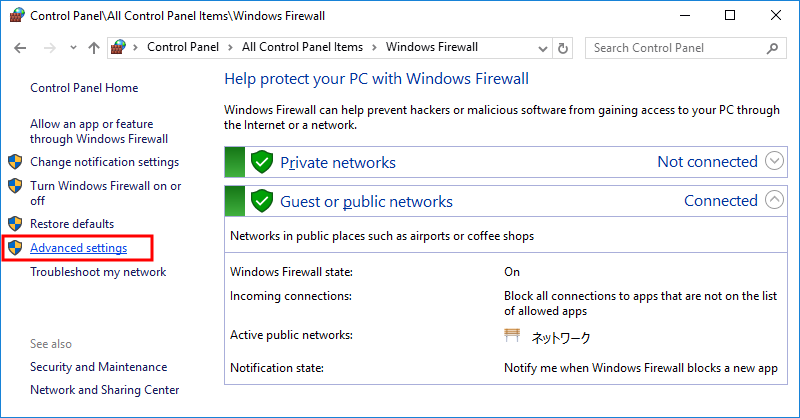
Left click the "Advanced Settings" link.
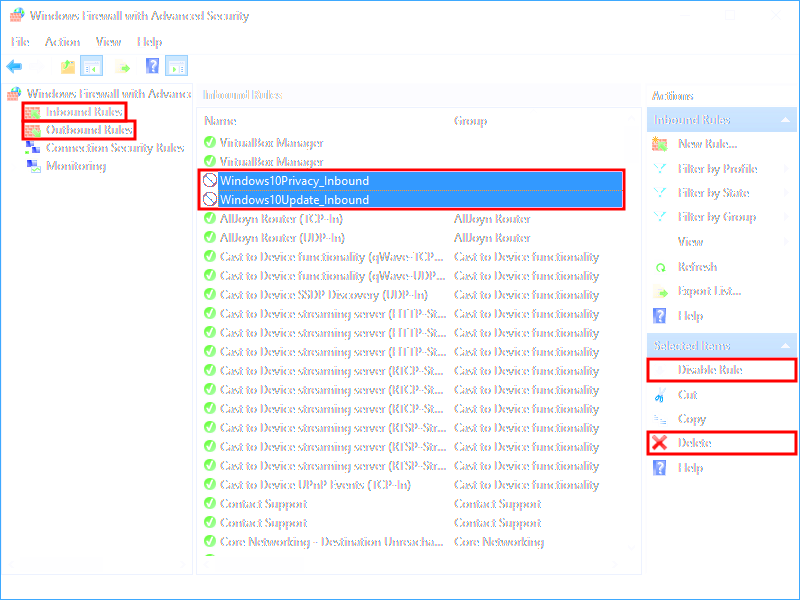
Select [Inbound Rules] or [Outbound Rules] on the left side.
Find and select "Windows10 Privacy_Inbound" or "Windows10 Privacy_Outbound" on the center.
If you want to disable the rule, click [Disable Rule] on the right side.
If you want to delete the rule, click [Delete] on the right side.
If you use Bing, delete 204.79.797.200.
- Right click the "Windows10 Privacy_Outbound".
- Select 204.79.797.200 and click [Delete].
- Click [Apply] and [OK]
Read also: Windows Update Filter
Hi there.
Could you please exlpain how were you able to extract all these malicious IPs?
Please, answer to my email.